Amazon S3 Malware Scanning Using Trend Micro Cloud One and AWS Security Hub | AWS Partner Network (APN) Blog

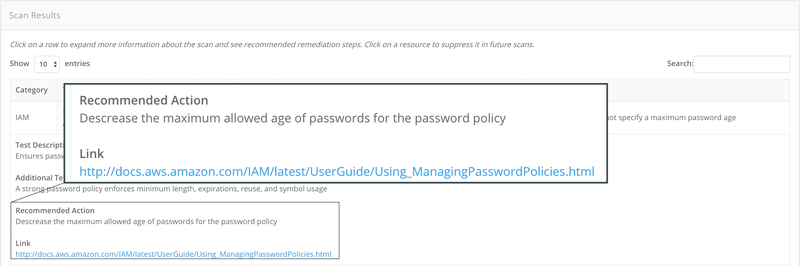
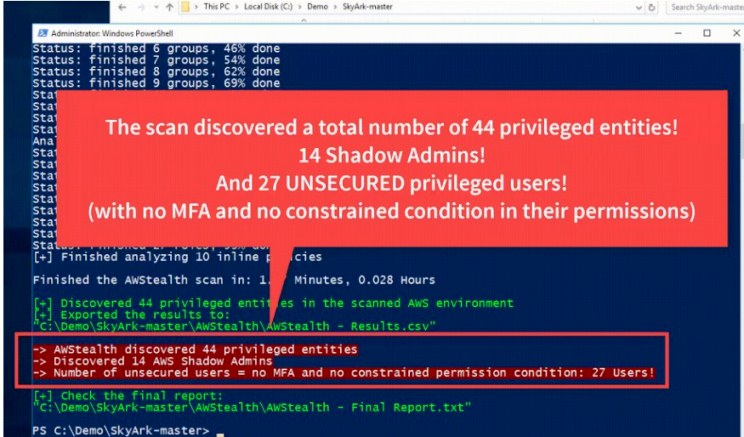
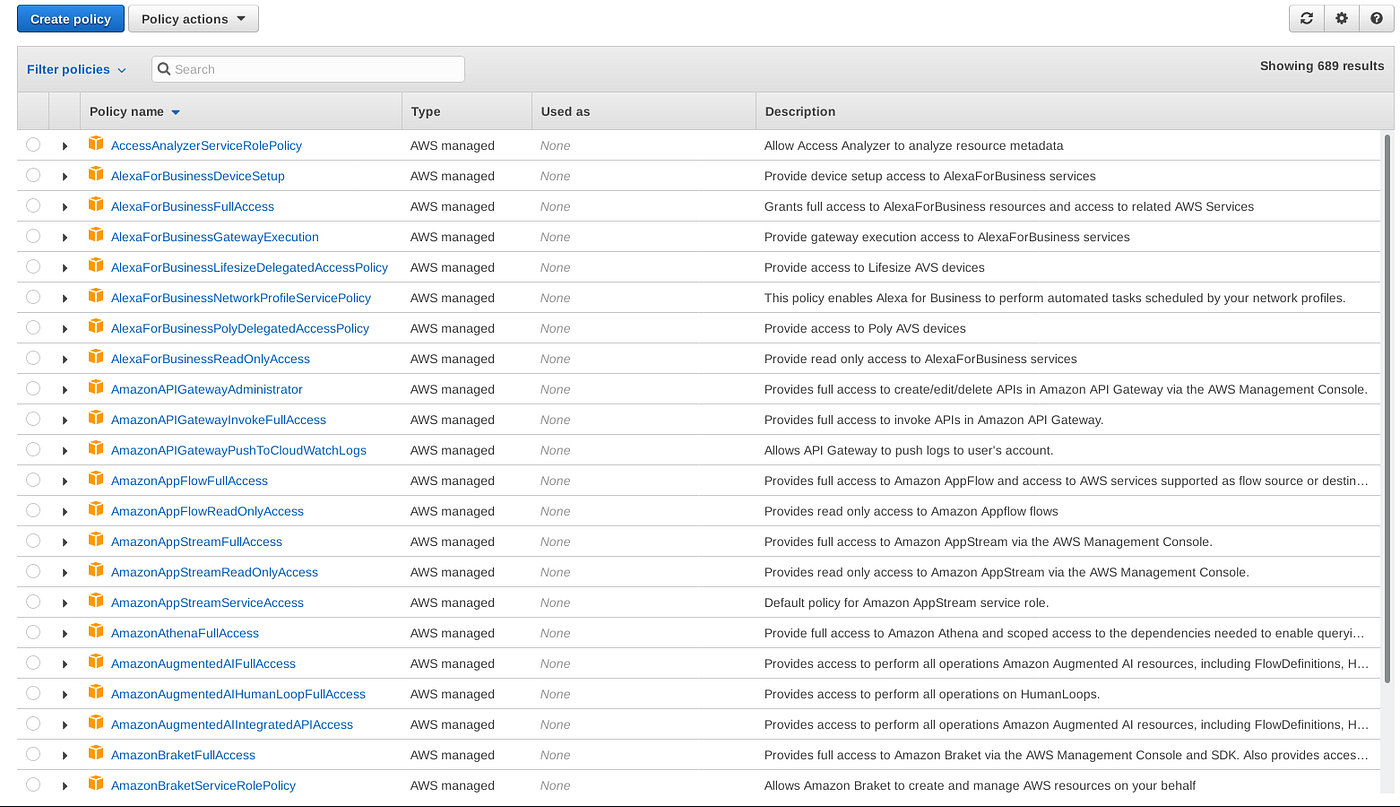
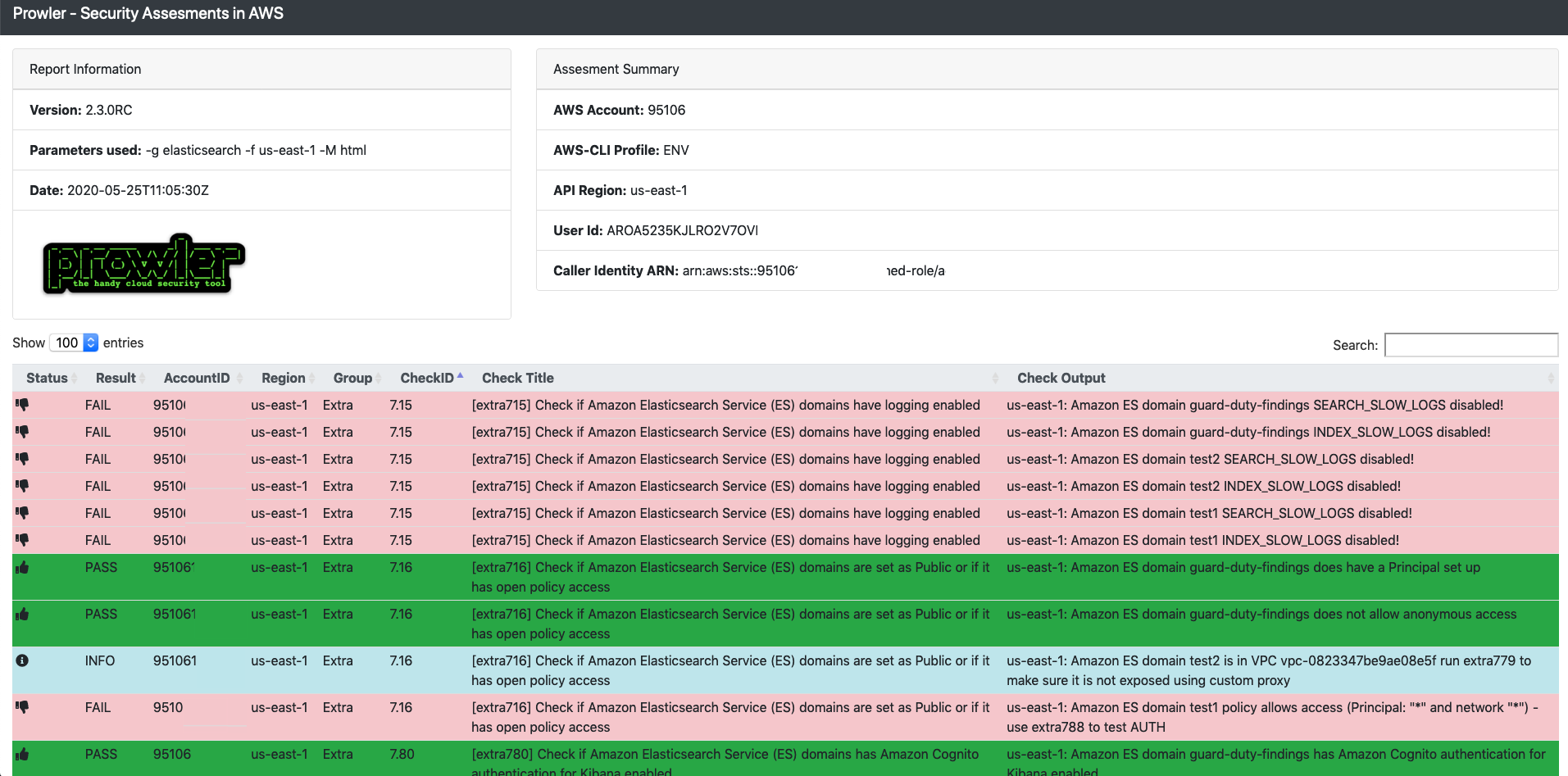
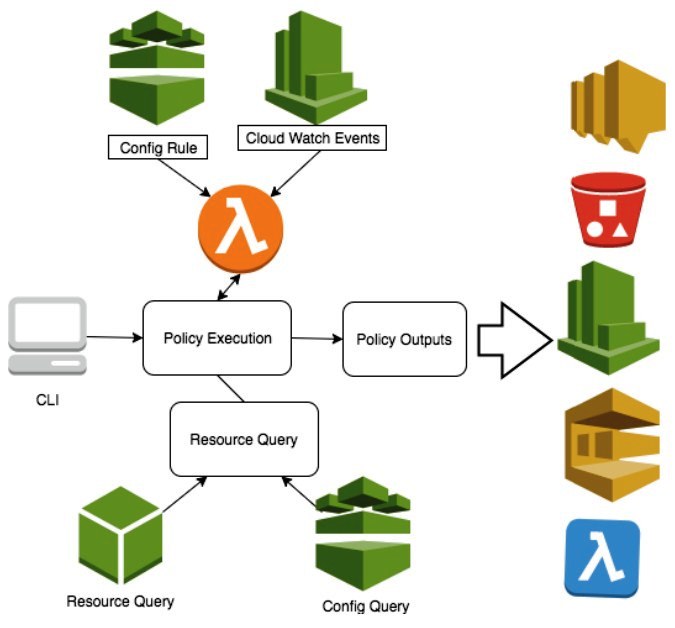
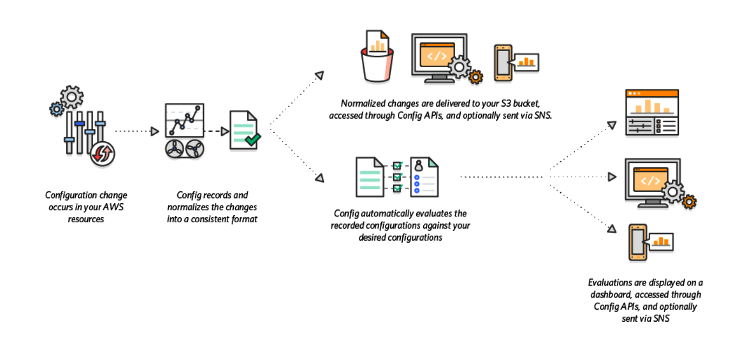
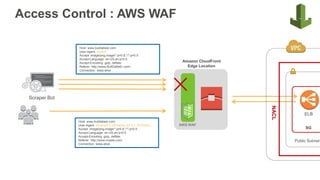
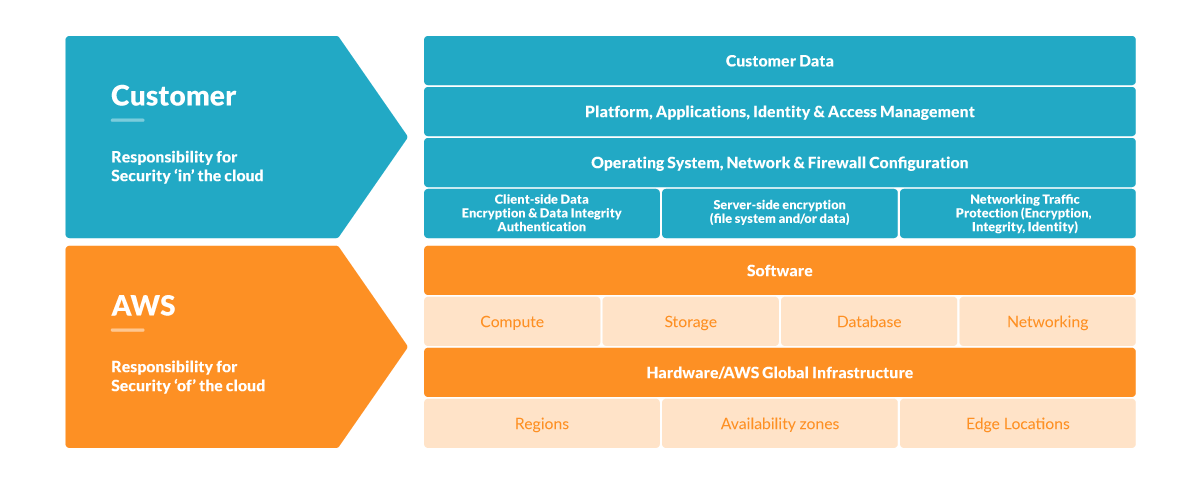
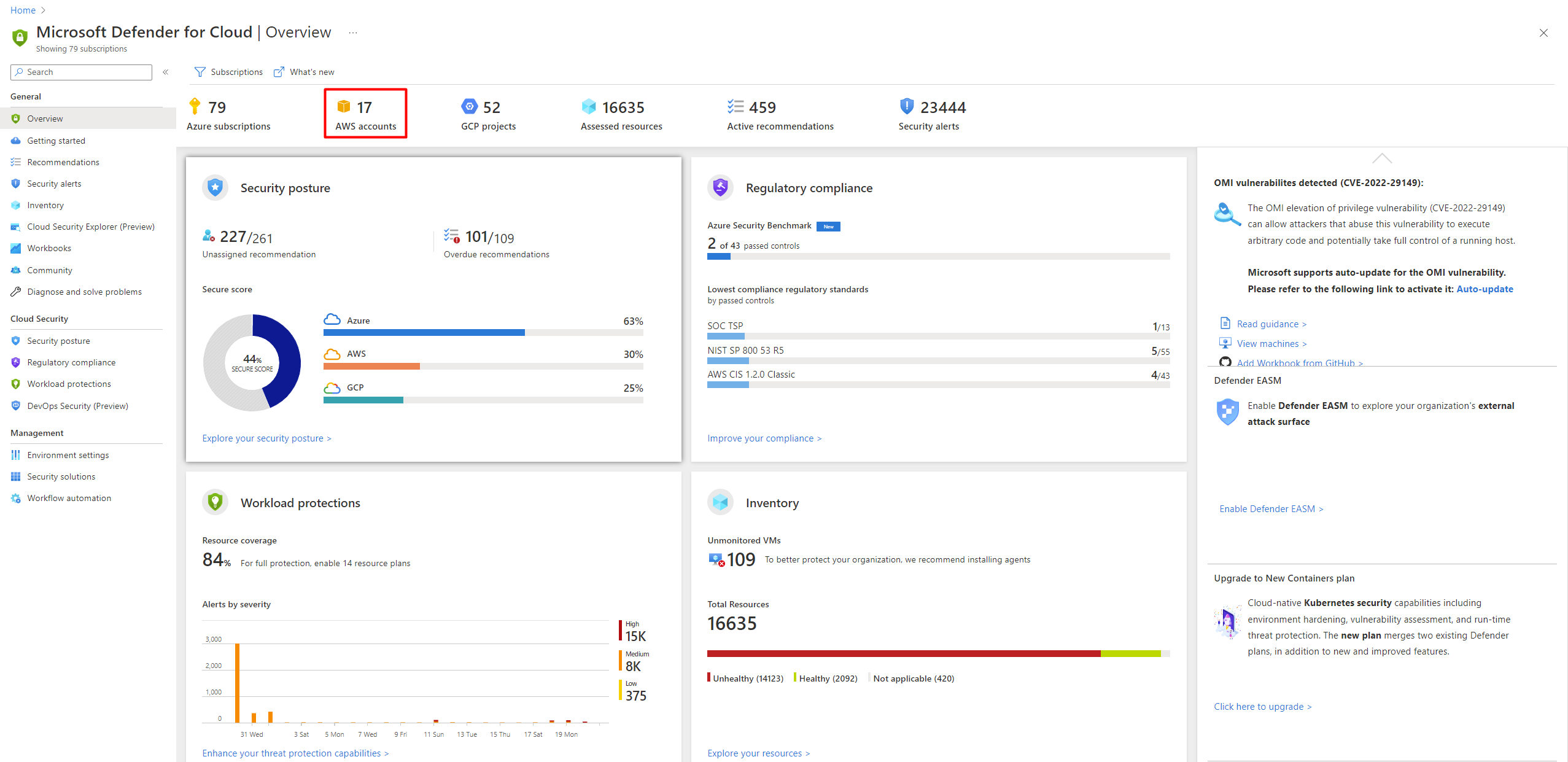
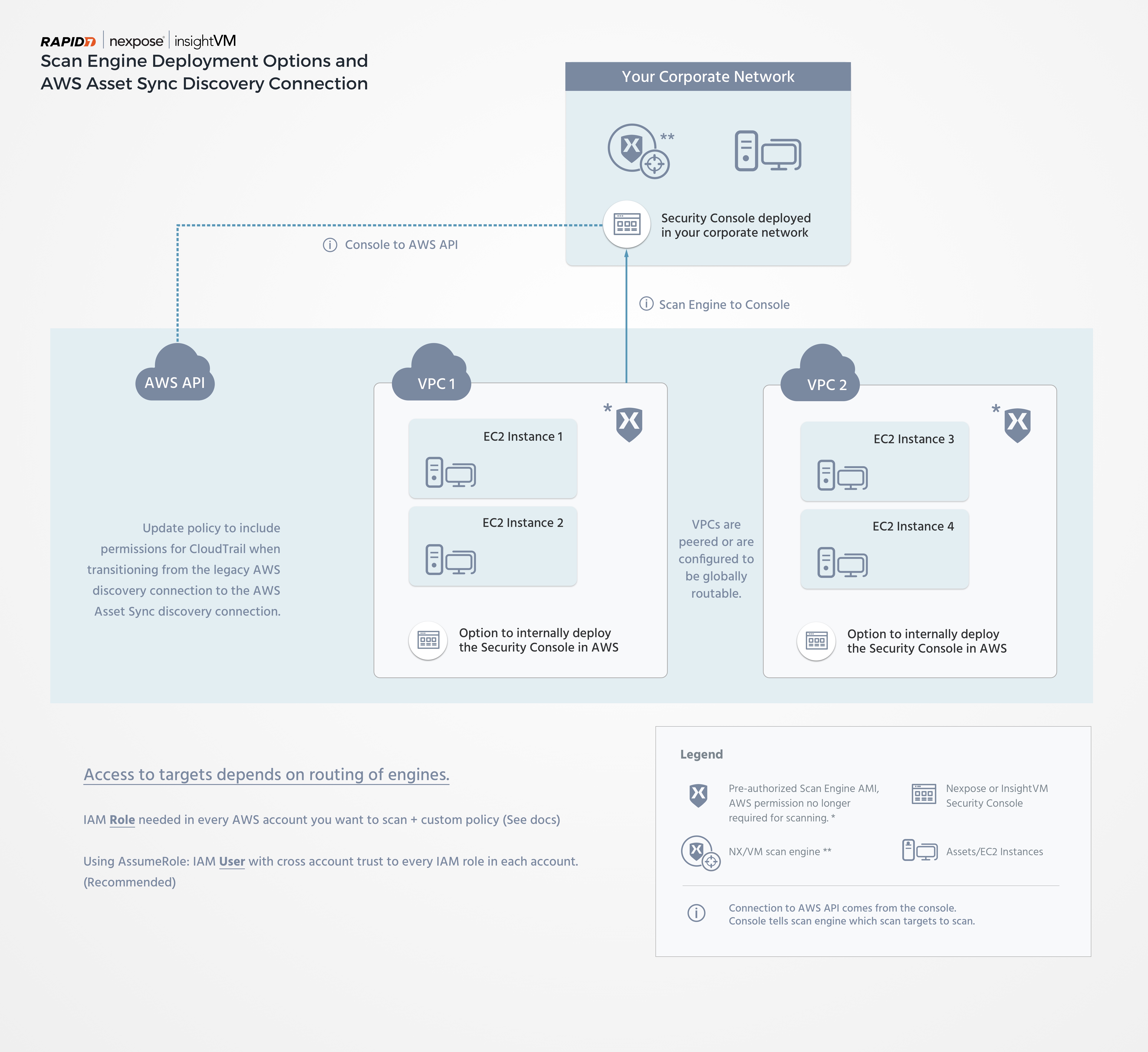
Top Security Scanning and Vulnerability Management Tools |AWS| | by Kubernetes Advocate | AVM Consulting Blog | Medium
Top Security Scanning and Vulnerability Management Tools |AWS| | by Kubernetes Advocate | AVM Consulting Blog | Medium
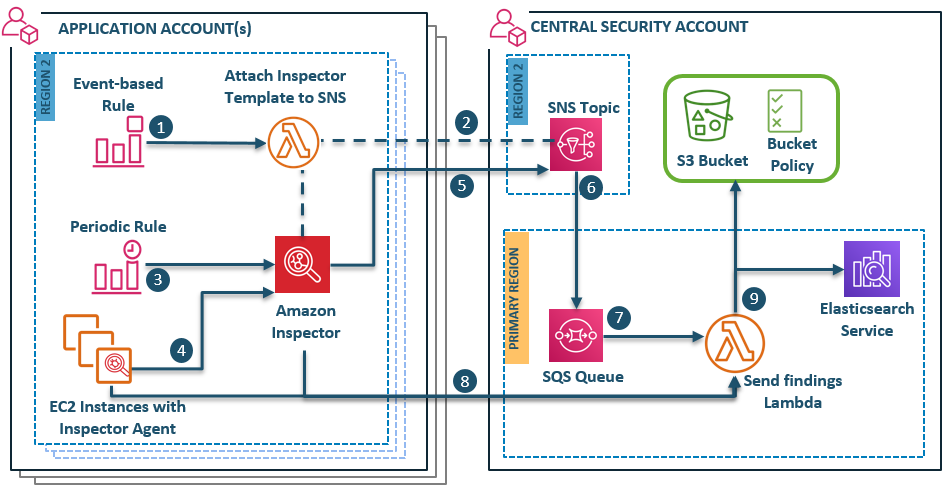
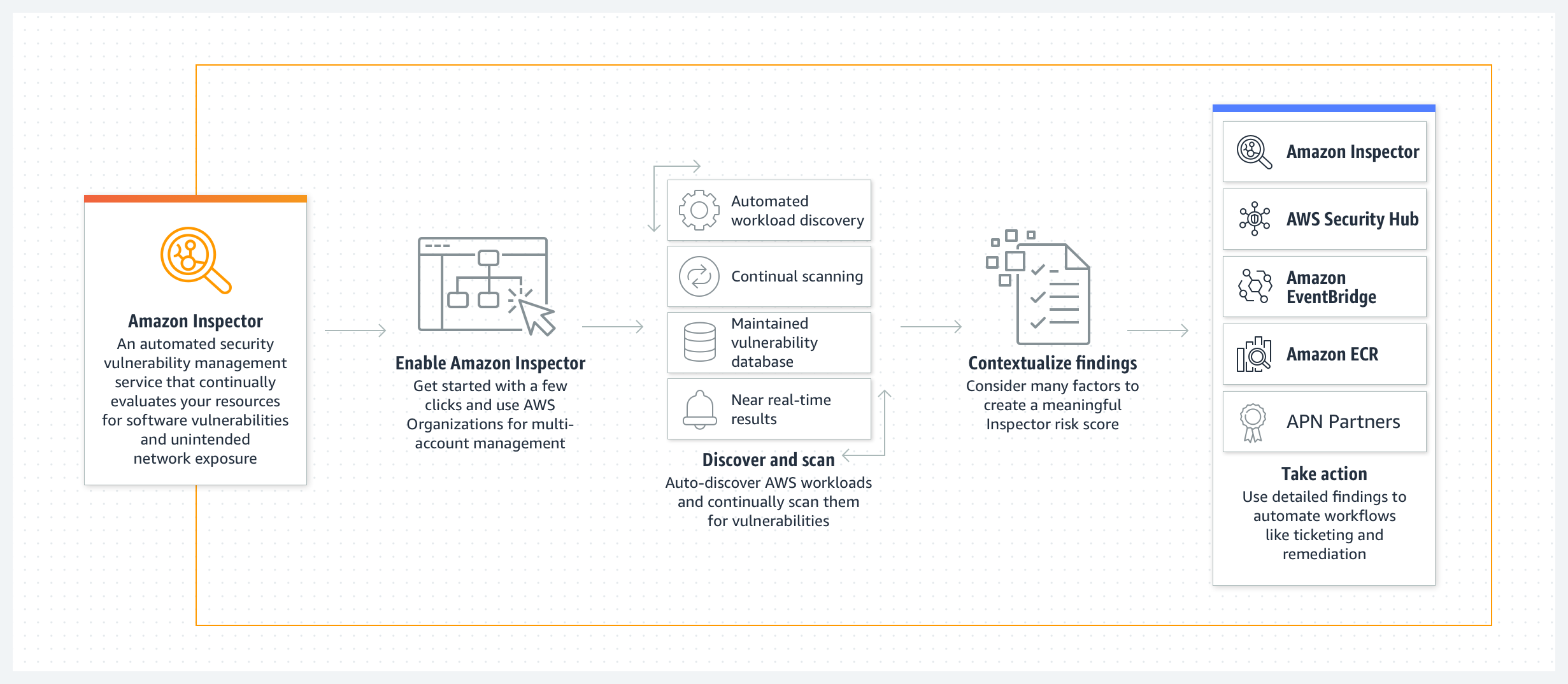
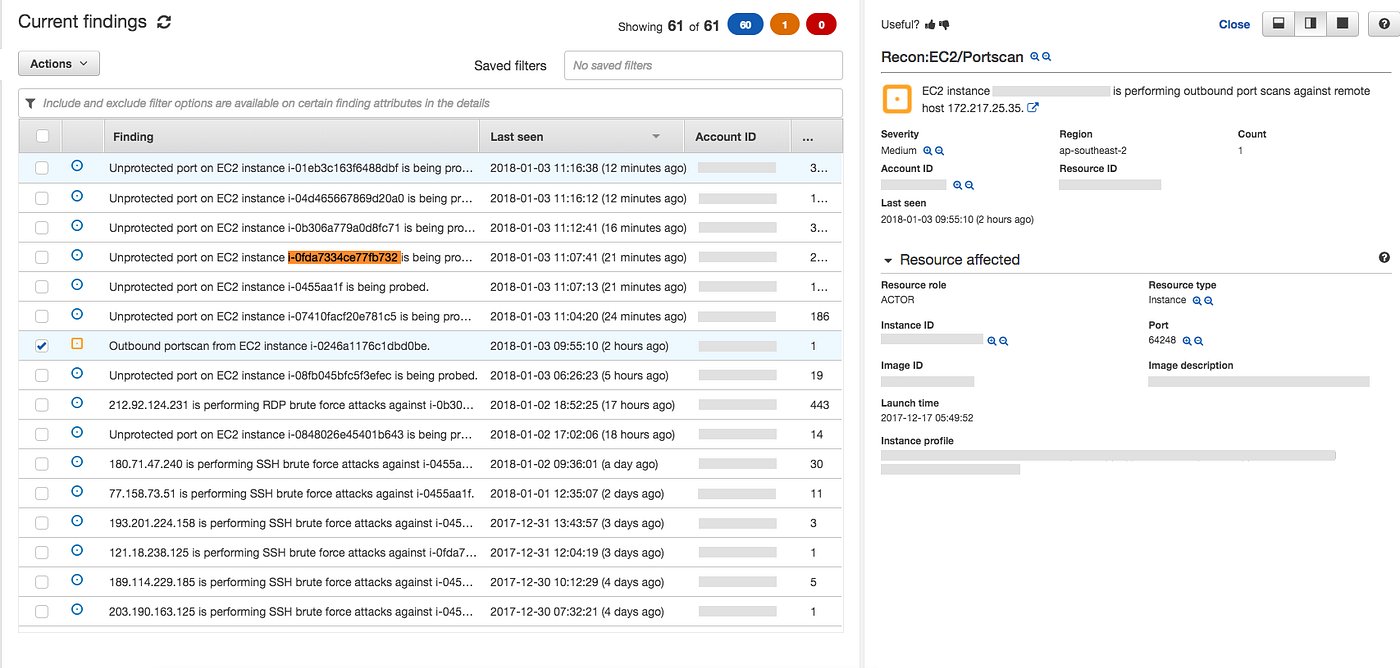
How to visualize multi-account Amazon Inspector findings with Amazon Elasticsearch Service | AWS Security Blog
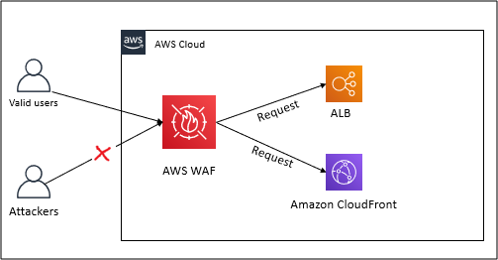
Top Security Scanning and Vulnerability Management Tools |AWS| | by Kubernetes Advocate | AVM Consulting Blog | Medium

How to Set Up Continuous Golden AMI Vulnerability Assessments with Amazon Inspector | AWS Security Blog