CVE-2019-19781, what you should know and how to fix your Citrix ADC, Access Gateway and SD-WAN WANOP - Poppelgaard.com

IoC Scanner shows if Citrix appliances have been compromised via CVE-2019- 19781 - Help Net Security

Bad Packets on Twitter: "Mass scanning activity detected from 100.33.141.194 (🇺🇸) checking for Citrix (NetScaler) servers vulnerable to CVE-2019-19781 and F5 BIG-IP servers vulnerable to CVE-2020-5902. #threatintel https://t.co/Yq1gFGUjoB" / Twitter

IoC Scanner shows if Citrix appliances have been compromised via CVE-2019- 19781 - Help Net Security
CVE-2019-19781, what you should know and how to fix your Citrix ADC, Access Gateway and SD-WAN WANOP - Poppelgaard.com
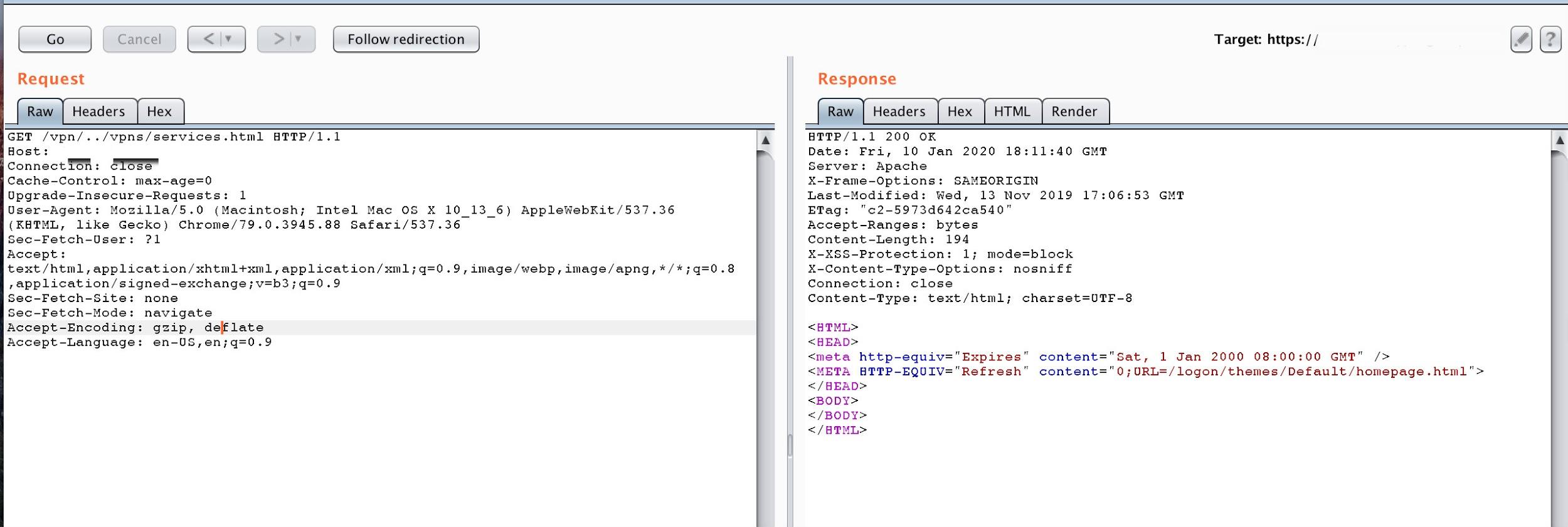
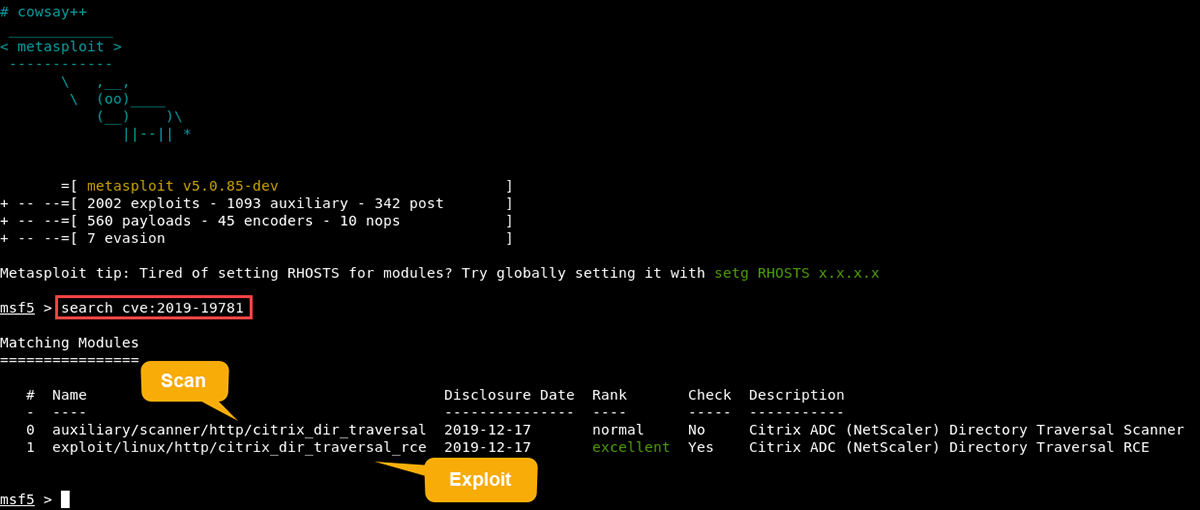
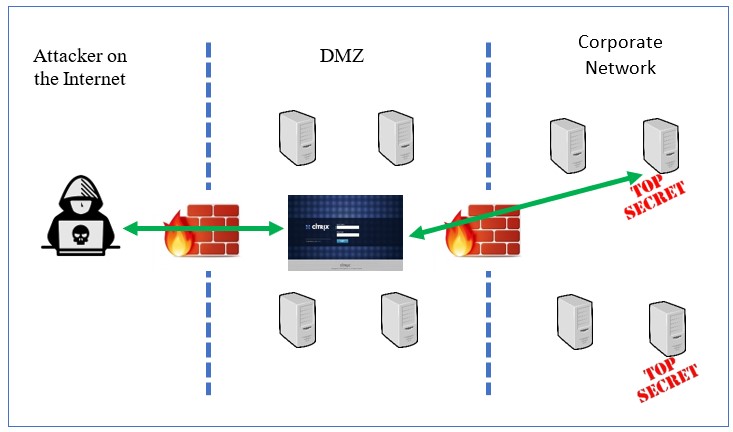
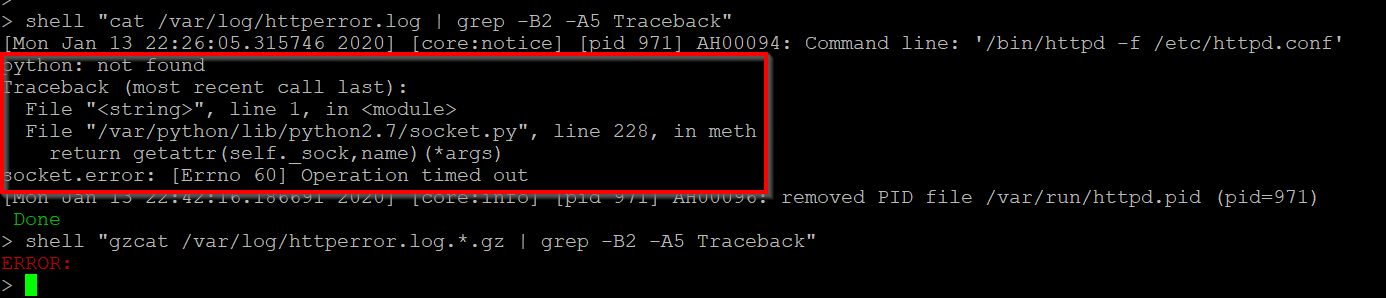
Exploits in the Wild for Citrix ADC and Citrix Gateway Directory Traversal Vulnerability CVE-2019-19781
CVE-2019-19781: Unauthenticated Remote Code Execution Vulnerability in Citrix ADCs and Gateways - Blog | Tenable®

Attackers exploiting critical Citrix ADC, Gateway flaw, company yet to release fixes - Help Net Security

Bad Packets on Twitter: "⚠️ 𝗪𝗔𝗥𝗡𝗜𝗡𝗚 ⚠️ Mass scanning activity detected from 156.17.191.239 (🇵🇱) checking for Citrix (NetScaler) Gateway servers vulnerable to CVE-2019-19781. Ports targeted: 443, 2083, 2087, & 8443/tcp Mitigation steps